The acquisition of different levels of security certification on a Supply Chain / Organization is a highly demanding process. In terms of applying and enduring the process, Supply Chains must be prepared adequately and act proactively by enforcing security properties. The role of primitive evidence collection in supply chains towards its certification is a crucial one. Primitive data, events that occurs on the basis of a supply chain are playing mandatory role when assuring the security aspects of the latter.
Security Assurance Certification Module (SACM) that has been introduced in FISHY includes two major components towards this direction. The auditing mechanism and the evidence collection engine. The evidence collection engine is the tool that, based on the collected data and triggering events, formulates a rule or a set of rules and pushes the latter towards the auditing mechanism module for evaluation. Data and events are collected through various sources such as ElastiSearch where lightweight shippers forward and centralize log data. Evidence collection engine is initiated on demand by the auditing mechanism. This tool is essential for the evidence auditing mechanism functionality due to the fact that it collects and feeds the essential information from the assets as events.
Auditing mechanism is a tool that can be used from a wide range of companies that plan to acquire certifications for cybersecurity properties. Specifically, this tool monitors those security properties that are set and produces a cybersecurity posture notion to ensure that these properties are well applied and interconnected with each other. It performs the former tasks by indicating the flaws in the applicability and by notifying the company for its cybersecurity status. After completing the process of conducting multiple assessments and reaching the requirements, the organizations may be ready for initiating the certification process.
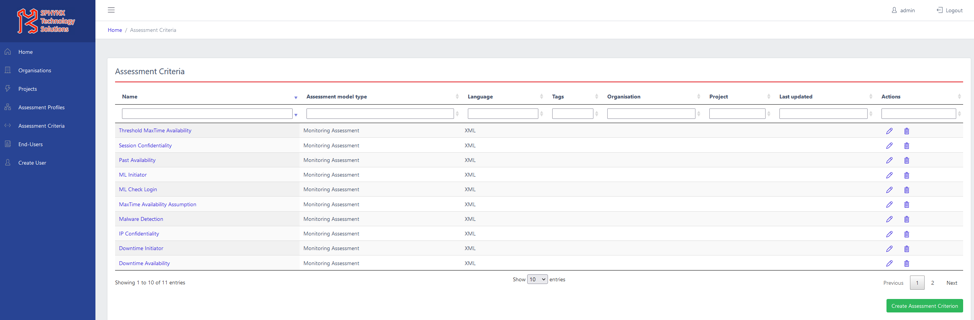
Control and results of the auditing procedure is being made though the SACM Graphical User Interface fully integrated in FISHY dashboard where end user may initiate the auditing procedure and observer in real time the evaluation procedure. The SACM GUI comes with a series of predefined security metrics covering the confidentiality, integrity and availability (CIA) principles witch together are considered the three most important concepts within information security.
Kalogiannis Grigorios (STS team)